Shodan is a search engine to find specific services such as webcams, SCADA systems, linksys…
Its operation is simple but effective: it scans the whole internet and uses the information returned by the device banners to discover the software version, the device model, etc.
Shodan is especially useful for the investigation of IoT devices, since there are millions of devices online with vulnerabilities that can be located by the information they provide in their responses.
Mode of use
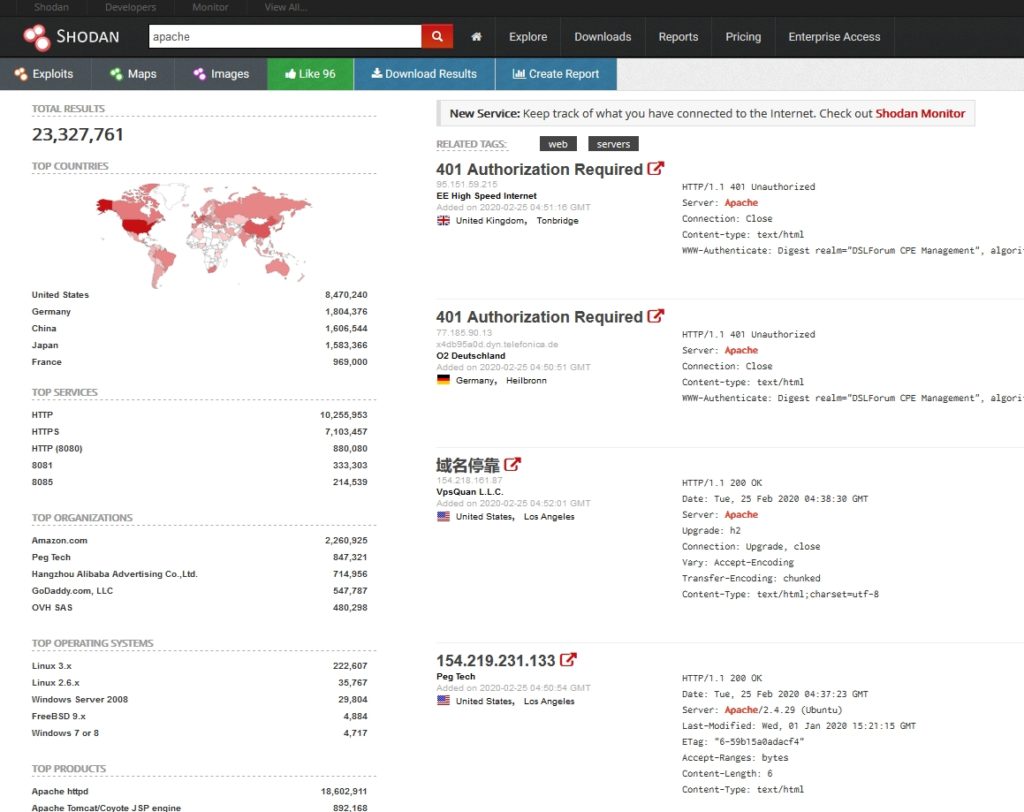
First, I’ll do a simple search. I’m going to look at the different Apache servers in the world. To do this, just type “apache” into the search engine.
On the left we can see the number of results. Shodan has 23 million servers indexed that use Apache. Below we can see a ranking of countries where these devices have been found.
Following with the left column, we can see the main ports where this service has been found. Since Apache is a web server, most of them have been found on ports 80 (HTTP) and 443 (HTTPS). But we can see that many others have been found on ports 8080, 8081 and 8085.
We are also shown the devices found according to the company that owns them, and according to the operating system that hosts them. All this data is obtained from the response that the service returns in the form of a banner when Shodan has scanned it.
In the right column we find the detailed information of the search results, showing IP, domain name, ISP, when it was last scanned, its location, and the very banner from where it has obtained the information.
Then, if we click on one of the results, we can see information in detail:
In this view we can see the information about the host, all the ports it has open, and the banners of all the services it has running. In addition, it shows us a list of known vulnerabilities that have been found in the server.
It is very important to understand that Shodan does not scan the whole Internet every time we perform a search (this would be literally impossible), but it performs a periodic scan, little by little, and what it shows us are the devices that fulfilled the characteristics of our search the last time they were scanned.
Therefore, it is possible that Shodan returns a result and when we go to check it, that service is no longer running on that port, or the software version has changed.
Filters
Like the google dorks, Shodan as a search engine also has keywords that we can use to refine our search. Below I show you the basic filters of Shodan:
It shows the services/devices that are in Madrid.
It shows the devices/services found in Spain.
It shows the devices/services found in Murcia (38,-1.1).
It shows devices/services with “google” domain name. For example, we can find all the Google Web Servers with the search “Server: gws” hostname: “google”
It shows the devices/services on the subnet 123.456.789.0/24.
It shows the devices/services with Windows 2003 operating system.
It shows the devices that have services running on port 22 (usually ssh).
A service can run on any port, but by convention this is the most common service/port list:
21 (FTP)
22 (SSH)
23 (Telnet)
25 (SMTP)
53 (DNS)
80 (HTTP)
81 (HTTP)
110 (POP3)
119 (NNTP)
137 (NetBIOS)
143 (IMAP)
161 (SNMP)
443 (HTTPS)
445 (SMB)
465 (SMTP)
623 (IPMI)
993 (IMAP + SSL)
995 (POP3 + SSL)
1023 (Telnet)
1434 (MS-SQL)
1900 (UPnP)
2323 (Telnet)
3306 (MySQL)
3389 (RDP)
5000 (Synology)
5001 (Synology)
5432 (PostgreSQL)
5560 (Oracle)
5632 (PC Anywhere)
5900 (VNC)
6379 (Redis)
7777 (Oracle)
8000 (Qconn)
8080 (HTTP)
8129 (Snapstream)
8443 (HTTPS)
9200 (ElasticSearch)
11211 (MemCache)
27017 (MongoDB)
28017 (MongoDB Web)
Displays all devices/services scanned in 2018.
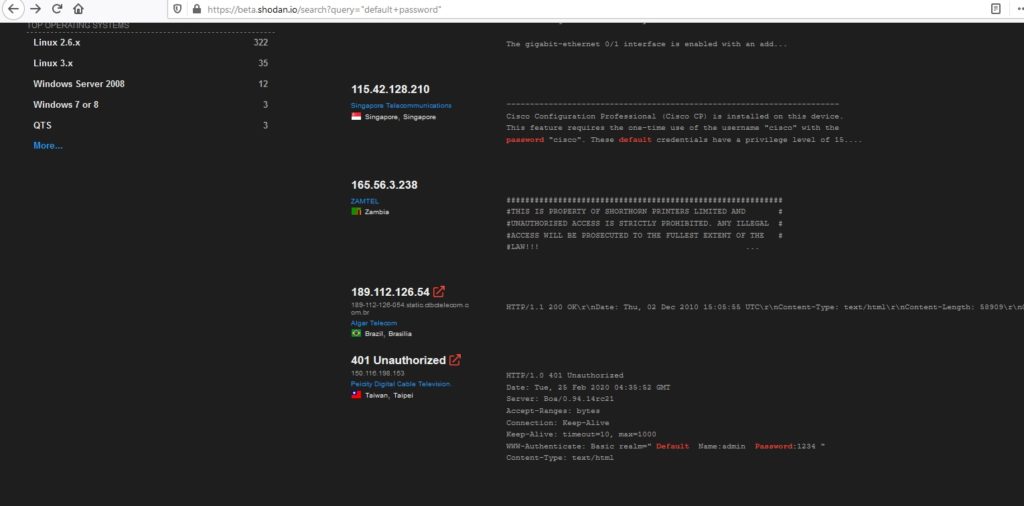
In the filters lies the true power of shodan. We can combine all these filters to get very specific results, and get very interesting information if we are doing a pentest or a red team exercise.
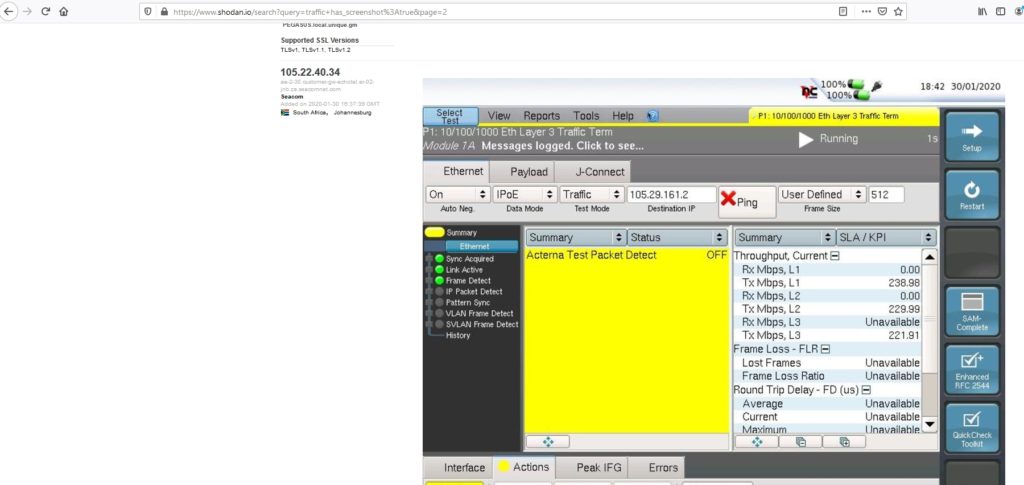
We can use Shodan to search for webcams, routers, SCADA systems (that control gas stations, power stations, nuclear plants)… Even traffic lights!
Here you can find a list of the most searched terms in Shodan. By registering you can perform a certain number of searches each day. If you are interested in performing more searches or want to use the Shodan API, you will need a Pro account.
Finally, remember that giving you this information is completely legal, but what you do with it may not be.
Lethani.



Ich habe Ihren Artikel mit Interesse gelesen. Anissa Bradford Ogren
Danke!
Das ist wirklich interessant. Sie sind ein sehr erfahrener Blogger. Ich bin Ihrem RSS-Feed beigetreten und freue mich darauf, mehr von Ihrem wunderbaren Beitrag zu erhalten. Außerdem habe ich Ihre Website in meinen sozialen Netzwerken geteilt! Ester Benn Robertson
Danke!
Es ist in Wirklichkeit eine nette und nützliche Information. Ich bin zufrieden, dass Sie uns diese nützlichen Informationen gerade mitgeteilt haben. Bitte halten Sie uns so auf dem Laufenden. Danke für das Teilen. Clemmy Bink Henning
Danke!
I have read several excellent stuff here. Definitely price bookmarking for revisiting. I wonder how so much attempt you place to make such a excellent informative web site.
Sasha Jerome Means
Thank you so much!
Merely wanna input that you have a very decent internet site , I the pattern it really stands out. Ella Vidovik Myron
Thank you!!
I’m gonna start using Shodan soon, it’s so cool
Really good post!!