CTF (Capture The Flag) events are becoming increasingly popular in the IT world. Every week there are meetings where computer security lovers meet to demonstrate their hacking skills.
And the way hackers are trained for these events are the CTF labs, websites where you can find hundreds of challenges of different categories: web, pwn, steganography, cryptography…
Hack The Box is one of these labs. Not only does it offer challenges, but entering it is a challenge in itself: you have to hack the web to get an invitation.
To hack the invitation, first go to…. Stop! There will be no spoilers in this post. While it may cost a bit at first, ctfs are a matter of honour. Before you ask for a clue or search the internet, try to do your best. If you don’t get through this challenge on your own, you will hardly be able to face the Hack the Box CTFs.
Once you get the invitation, you’ll find something like this:
***EDIT: HackTheBox Interface has changed recently. You can see the latest introduction to HackTheBox in this post.***
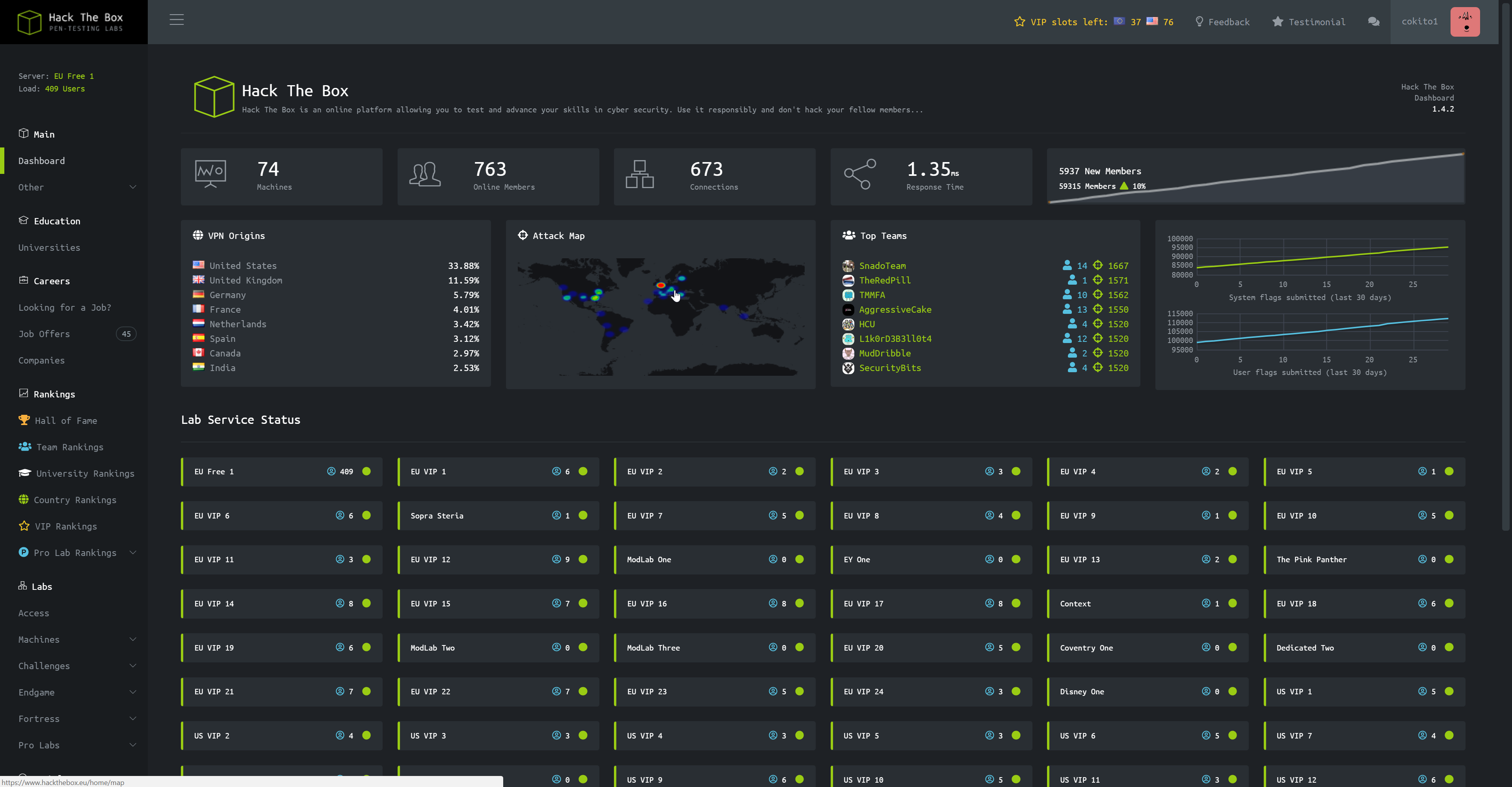
I remember when I got in, there was so much information I had no idea what to do. Little by little you will discover what each thing is, but for the moment you only have to worry about the left side panel. Specifically, in the Labs part.
Hack The Box is essentially divided into two parts: Machines and Challenges.
Machines
The machines are the essence of the page: they are real virtualized machines that you must exploit to get the user flag and the root flag. Each flag is in the respective home folder. It’s as simple as that.
The connection to the machines is made by means of a vpn. To create it, you must go to Access and download the file user.ovpn, open a terminal in linux and write where you downloaded it:
$> openvpn user.ovpn
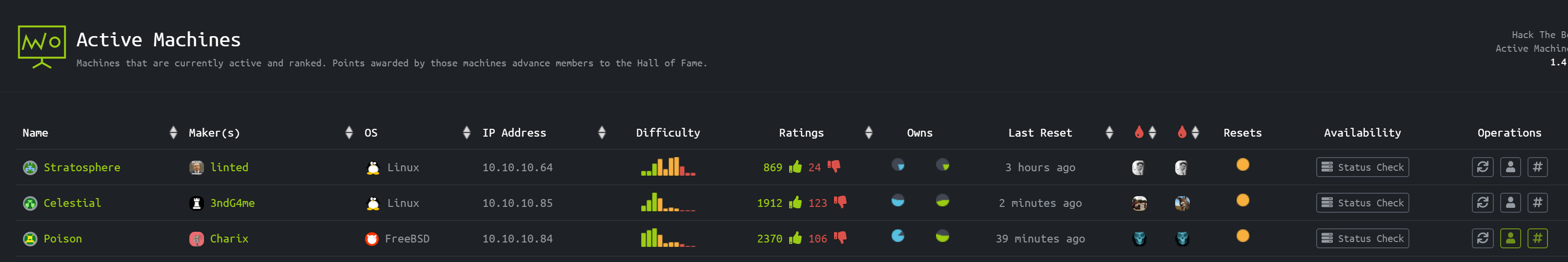
Once the connection is established, you only have to go to Machines -> Active and choose the IP of the machine you want to exploit. The rest is up to you.
I recommend you start with the ones with the very green “Difficulty” graph. Once you get the user and root flag (they are always a hash), you must enter them in the “Operations” section and they will add up the points. If you score a lot of points, you can get into the Hall of Fame, and be as famous as the OscarAkaElvis himself!
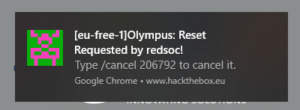
In case you touch what you don’t need and want to reset the machine, you can do it in the “Operations” section too. But beware, the machines are shared among Hack The Box users, so if you’re about to get the root flag and another user restarts the machine, you’ll have to start over.
To avoid this, go to Social -> Shoutbox. A message will appear when someone asks for a machine restart, and you will have two minutes to cancel that restart by typing /cancel. Turn on notifications on browser so you don’t have to constantly check it:
Challenges
Challenges are often simpler and quicker to make than machines. You don’t need a vpn for do a challenge. So I think it’s a good option to start here. There are currently 8 different types of challenges:
– Reversing: reverse engineering. It consists of disassembling an executable to obtain the source code of the application.
– Crypto: cryptography. The challenges are based on questioning your ability to break encryption.
– Stego: steganography. It consists of hiding messages inside texts, images, audios… so that they go unnoticed. If you want to know more about steganography, you can read my post “Steganography: the art of hiding”.
– Pwn: to get the flag, you must compromise the safety of whatever you are given and become its owner and lord.
– Web: web hacking challenges. SQL injection, XSS, and much more.
– Misc: a bit of everything. You don’t know what you can find.
– Forensics: you will have to use computer forensic techniques to discover the flag of the files.
– Mobile: hacking of mobile applications.
All challenges are to find out the flag, which always has the format HTB:{s0m3_t3xt}.
With this post you have everything you need to get started in the world of CBC’s. In subsequent blogs, I will explain different techniques that can be used to solve challenges and machines.
Lethani.

took me an hour to get the invite code, never thought of even asking for help it was fun and simple nice blog post i ended up jumping right into the machines started with mischief been 1 day and stuck at the 2nd login screen LOL will figure it out hack the box is an awesome site
Hahaha thanks! Yes, it is an awesome and fun site!
Woah it help me, thank you!
Nice blog